In an era where digital transformation defines how organizations operate, protecting sensitive data and systems has become a top priority. From financial institutions to small online businesses, identity-based threats such as phishing, credential stuffing, and account takeovers continue to rise. As remote work, cloud computing, and online transactions expand, companies need robust solutions to verify user identities and prevent unauthorized access. Identity verification applications play a crucial role in strengthening security, reducing fraud, and building user trust.
TLDR: Identity verification apps help organizations prevent unauthorized access by confirming users are who they claim to be. They use technologies such as biometric authentication, document verification, AI-driven fraud detection, and multi-factor authentication. Choosing the right app depends on your business size, compliance needs, and security goals. Below are five powerful identity verification apps that enhance protection and streamline authentication processes.
Identity verification solutions go beyond passwords. They combine advanced technologies such as facial recognition, optical character recognition (OCR), liveness detection, and encrypted authentication to ensure that user identities are legitimate. Below is a closer look at five trusted apps that help prevent unauthorized access.
1. Okta Verify
Best for enterprise-level identity and access management
Okta Verify is part of Okta’s broader identity and access management ecosystem. It provides secure multi-factor authentication (MFA) to verify user identities before granting access to applications, networks, or devices. Designed primarily for businesses, it integrates seamlessly with cloud platforms and enterprise software.
Key features include:
- Push-based authentication for quick approvals
- Biometric sign-in options such as fingerprint and facial recognition
- Integration with thousands of enterprise applications
- Adaptive authentication based on risk scoring
Okta Verify reduces password reliance and protects systems even if a password is compromised. Adaptive MFA analyzes contextual data such as device type, location, and behavior patterns to determine whether additional authentication steps are required. This proactive approach significantly lowers the risk of credential-based attacks.
For larger organizations handling sensitive data, Okta Verify provides both scalability and compliance support.
2. Jumio
Best for AI-powered identity proofing and KYC compliance
Jumio specializes in digital identity verification, particularly for industries such as banking, fintech, healthcare, and online marketplaces. It combines artificial intelligence, machine learning, and biometric technology to verify government-issued IDs and match them to user selfies.
Core capabilities:
- Automated ID document verification
- Facial recognition with liveness detection
- AML and KYC compliance tools
- Real-time fraud risk analysis

Jumio’s liveness detection ensures that attackers cannot bypass verification with printed photos or recorded videos. It checks for subtle facial movements and environmental cues to confirm the user is physically present. This capability is essential in preventing identity spoofing.
With regulatory pressures increasing worldwide, Jumio also helps organizations comply with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations. Its AI-driven verification processes speed up onboarding while maintaining strict security standards.
3. Authy
Best for user-friendly multi-device authentication
Authy, now part of Twilio, is a popular two-factor authentication (2FA) app that enhances security for both individuals and businesses. Unlike traditional SMS-based 2FA, Authy generates secure time-based one-time passwords (TOTP) that remain safe even if mobile networks are compromised.
Top benefits:
- Secure cloud backup of tokens
- Multi-device synchronization
- Offline authentication support
- Strong encryption protocols
One of Authy’s distinguishing features is its multi-device capability. Users can securely access their authentication tokens across smartphones, tablets, and desktops without sacrificing security. Encrypted backups ensure that users do not lose access if a device is damaged or replaced.
Authy’s simplicity makes it ideal for startups and small businesses seeking stronger authentication without deploying complex identity management systems.
4. Microsoft Authenticator
Best for integration within Microsoft ecosystems
Microsoft Authenticator is widely adopted due to its seamless integration with Microsoft 365, Azure Active Directory, and enterprise security frameworks. It supports passwordless login, significantly reducing the risk of phishing attacks.
Main features include:
- Passwordless authentication
- Push notifications for account approval
- Biometric unlock options
- Account activity notifications

Passwordless authentication is a major advancement in identity security. By removing passwords entirely and replacing them with biometric data or secure device-based approval, organizations reduce their vulnerability to phishing, brute force attacks, and credential reuse.
Additionally, Microsoft Authenticator provides real-time alerts when suspicious login attempts occur. This immediate visibility enables organizations to respond quickly to potential breaches.
5. ID.me
Best for secure identity verification in government and healthcare
ID.me focuses on high-assurance identity verification for government agencies, healthcare providers, and financial institutions. It employs a multi-layered identity proofing system that combines biometric analysis, document review, and database validation.
Highlights of ID.me:
- Video chat verification with trained agents
- Government-grade identity proofing
- Secure digital identity wallet
- Compliance with federal standards
One of ID.me’s differentiators is its live video verification process. In cases requiring elevated assurance, users can interact with a trained agent who verifies their identity in real time. This adds an additional layer of protection for high-risk transactions or sensitive accounts.
ID.me’s digital wallet allows users to reuse verified credentials securely across participating platforms, reducing repetitive verification while maintaining strict security standards.
How Identity Verification Apps Prevent Unauthorized Access
Identity verification apps work by implementing layered security controls. Rather than relying on a single authentication factor, they combine multiple elements:
- Something you know: Passwords or PIN codes
- Something you have: Mobile device or security token
- Something you are: Biometric data such as fingerprint or face recognition
This multi-factor approach drastically reduces unauthorized access risks. Even if one factor is compromised, attackers would still need additional authentication components to gain entry.
Many apps also incorporate behavioral analytics. These systems evaluate login patterns, location data, device metadata, and typing behavior to detect anomalies. When suspicious activity is identified, the app may request additional verification or block access altogether.
Choosing the Right Identity Verification App
Selecting the right solution depends on several factors:
- Business size: Enterprises may require robust identity management ecosystems like Okta, while smaller organizations might benefit from simpler solutions like Authy.
- Compliance requirements: Regulated industries often need AI-powered document verification and AML compliance tools.
- User experience: Seamless authentication minimizes user friction and improves retention.
- Integration needs: Compatibility with existing systems ensures smooth deployment.
- Security goals: Passwordless solutions and biometric features may provide higher levels of protection.
Security should never come at the cost of usability. The most effective identity verification apps strike a balance between strong protection and smooth user interaction.
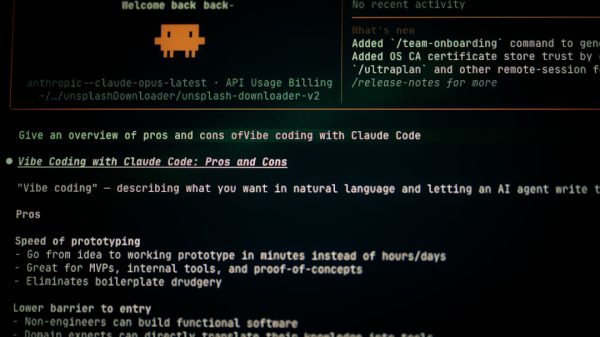
The Future of Identity Verification
As cyber threats evolve, identity verification technologies continue to advance. Artificial intelligence, decentralized identity models, and blockchain-based credentials are shaping the future of digital identity management.
Passwordless authentication is likely to become the norm, while biometric accuracy continues to improve. Organizations that adopt modern identity verification apps position themselves to combat unauthorized access more effectively and safeguard customer trust.
FAQ
- What is an identity verification app?
An identity verification app is a security tool that confirms a user’s identity before granting access to systems, accounts, or transactions. It often uses multi-factor authentication, biometrics, and AI-driven analysis. - How do identity verification apps prevent unauthorized access?
They require multiple authentication factors such as passwords, devices, and biometric scans. Many also monitor behavior and detect suspicious activity, blocking or flagging potential threats. - Are biometric methods safe?
Yes, when implemented securely, biometric methods such as facial recognition and fingerprint scanning are highly secure. Most apps encrypt biometric data to prevent misuse. - Which industries benefit most from identity verification apps?
Banking, healthcare, ecommerce, government, and fintech industries benefit significantly due to their high exposure to fraud and strict compliance requirements. - Can small businesses use identity verification apps?
Absolutely. Many apps offer scalable solutions suitable for small businesses, helping them strengthen security without requiring complex IT infrastructure. - Is passwordless authentication more secure?
In many cases, yes. Passwordless authentication eliminates weak or reused passwords, significantly reducing phishing and credential-based attacks.