Nowadays technology is replacing everything. In this advanced age of digital world, where we face much progress as well as we see many cons, you can have the ultimate check stub template for payroll with you, instead of having a perforated bit of paper attached to a physical cheque when paying your employees. Technologies are making work faster, with less manpower. On the other hand, it is also increasing cybercrime. In 2020, there were 4000 cyber-attack we have faced during COVID-19.
As technology is becoming revolutionary with every passing day, we are also renovating cybersecurity. In this digital world, we came across thousands of people without knowing them, and verifying the identity of the person with whom we are dealing is obligatory. Worldwide cybersecurity is envisioned to grow from $149.46 billion in 2019 to $152.21 billion in 2020 at a compound annual growth rate (CAGR) of 1.83%.
Challenges Faced By ID Verification Solutions:
Identity verification is necessary, but what is the ultimatum that we are facing for the IDV solution? Nowadays, there exist such identity verification services that are quite costly without any assurance of accuracy and efficiency, lacking with data management and reliability. In such circumstances customer satisfaction is mandatory. For identity verification, we have to be vigilant because it’s a sensitive sort of verification.
5 innovative Identity Verification Strategies
Below are 5 well-known strategies that we have to be aware of while conducting identity verification.
- Incorporation of Blockchain for seamless IDV
Blockchain uses identity verification to eradicate data misplacement, data security, data management, and several other reasons. There are a lot of cases that we face related to data mismanagement, our most of the data identification stored in a centralized place which makes it more appealing for hackers.
The identification breach is the most targeted kind of data breach among all. According to researchers, personal identification is 97% of breaches compared to other breaches in US.
As a result of rapidly evolving digitalization, the certainty of Personally Identifiable Information (PII) is demanded. In crypto, the emergence of blockchain technology makes it the most secure way. Blockchain is using cryptocurrency which is a decentralized method of transferring bitcoin and another crypto from one end to another, and that is end-to-end encrypted. Blockchain is using the IoT (internet of things) security system for recording data and data verification. It’s a huge phase of security systems, in which various algorithms are used to secure the whole system and make it next to impossible for hackers.
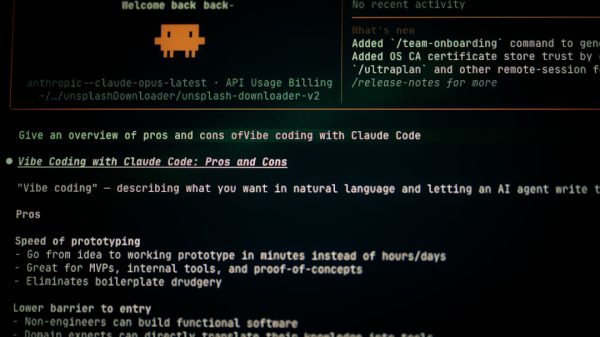
- Indulging AI solutions to combat identity theft
Identity theft is a common crime that is extending every passing day. Due to the pandemic, identity theft is an up-pacing crime worldwide. The cases reach up to 1,387,615 in the US which is thrice the cases in 2018. It’s a very effortless way of crime. Artificial intelligence is one of the sources to detect identity theft. To get rid of it, AI is the ultimate solution, which makes it impossible to get hacked.
Artificial intelligence is the only machine learning that is used to battle identity theft. As human power is costly and has more chances of error, on the other hand, AI code is much more secure and less costly. This means once the problem is identified it takes less than a minute to solve it globally. AI is the world’s most secure way to protect a large amount of data.
- How to analyze identity theft through OCR:
Optical character recognition (OCR) is used to extract data from any hard form of data. There are many types of OCR that are in use for identifying the identity of a person or a document.
Intelligent Word Recognition (IWR)
Intelligent Character Recognition (ICR)
Optical word recognition (OWR)
These all types are used to identify documents in various ways, i.e. handwriting, typewriting text, cursive text. OCR software is used to secure documents and helps to identify the source of documents. As the world is moving towards digitalization, which increases higher chances of cybercrime. OCR is one of the most important ways to secure identifying theft.
- Machine learning protection on identity theft:
Artificial intelligence algorithms are incorporated for the detection of identity theft. Machine learning is a subset of artificial intelligence. The implementation of artificial intelligence is machine learning. It is used to avoid human error, it can help to solve problems globally with less period of time. It helps computers to act like humans effortlessly. It takes the data from past searches and helps to find out future queries. But the question is how machine learning is helping us to combat identity theft?
Machine learning is used to detect identity theft, due to its method of encoding and decoding it’s hard to get hacked. Many organizations face various ID theft, and to get rid of it they use numerous technologies.
- Biometric verifying the identity:
Undoubtedly, hackers can hack someone’s data but they cannot hack someone’s biometrics. Secure biometric authentication involves the validation of customer’s demographics with a high rate of accuracy and efficiency.
AI-powered biometric authentication utilizes 3d liveness detection for quick and secure user authentication using a selfie of the user. Biometric login eliminates frictions and delays and easing the login procedure. 3D liveness detection captures live biometric data for accurate and effective matching. This provides a strong shield of protection to financial infrastructures against spoofing attacks and fraudulent activities. Biometric authentication platforms are capable of integrating with any platform with quick and easy developer options. The biometric authentication procedure is fast yet reliable with the help of AI-powered mapping techniques.
Conclusion:
There exists a wide range of products and services out there that provides reliable, real-time, accurate, and efficient identity verification solutions. Businesses must integrate themselves with trustworthy identity verification solutions to combat chargebacks and counterfeit activities. Enhancement of security protocols is the dire need of the hour. Financial infrastructures must take advantage of AI-powered identity verification solutions and must implement appropriate checks to combat illicit money transfers, identity theft and to differentiate between good and bad customers.