Rapid advancements in technology and the widespread adoption of digital systems have brought about new opportunities for growth and efficiency. At the same time, these advancements have also opened the doors to many cybersecurity threats that can jeopardize the confidentiality and integrity of sensitive data.
Over the last few years, cyber-attacks have wreaked havoc, caused significant financial losses, and damaged the reputation of many brands. According to the Data Breach Investigative Report by Verizon, 83% of the data breaches were perpetrated by external forces motivated by money. Around 74% of the breaches were due to human misuse, errors or social engineering attacks.
With more businesses relying on digital platforms, cloud services and the Internet of Things (IoT), cybercriminals are using different methods to gain access to sensitive data. When cyber-attacks are successful, they have devastating and long-lasting impacts on businesses. They can adversely affect business operations, undermine the sustainability of the business, and lead to customer distrust. This is the reason why many companies are now focusing on shoring up their cybersecurity.

According to the US Bureau of Labor Statistics, the demand for information security analysts will grow by 35% from 2021 to 2031. This rate of growth is faster than other occupations. With more companies looking for cybersecurity services, there is no better time to pursue a career in this field.
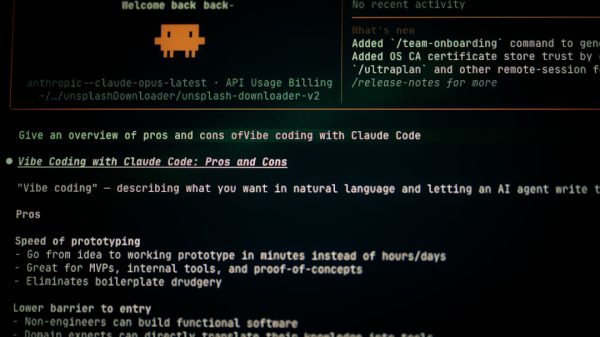
In the last few months, many people have been worried about AI taking over their jobs. This is something that you will never have to worry about if you become a cybersecurity specialist. Of course, you will want to know how to become a cybersecurity specialist. Most businesses look for cybersecurity experts who have the right education, knowledge and skills. So, enrolling in a cybersecurity program is the way forward. St. Bonaventure University offers an online Master’s of Science in Cybersecurity.
Even if you have no experience, you can join this program after completing the university’s cybersecurity foundation course. This master’s program is completely online and does not require GMAT or GRE. It builds proficiency in cloud security, secure software design, penetration testing, data mining, machine learning and AI, and networking, among others. The master’s degree curriculum teaches you to design, implement and assess security solutions, allowing you to transform into a cybersecurity specialist. Once you complete this two-year program, you will be skilled enough to help organizations with their cybersecurity needs.
Since cyber threats are on the rise, businesses, both big and small, need to focus on cybersecurity. However, most organizations do not understand cybersecurity and how to implement the right security measures. This is where a cybersecurity specialist comes into the picture. As an expert, you can help organizations to boost their cybersecurity defenses.
Perform a thorough cybersecurity assessment
Before you can help your organization improve its cybersecurity, it is crucial to know more about the latest threats, attack vectors and industry trends. When you know the techniques and tactics that cybercriminals use, you can anticipate potential risks and threats.
Then, it is time to identify potential weaknesses and vulnerabilities in the organization’s systems and processes. For this, you must conduct a comprehensive evaluation of the digital infrastructure and practices. This will enable you to pinpoint areas that could be susceptible to cyber-attacks.

Check the network architecture, data storage, hardware and software configuration, access control mechanisms, transmission mechanisms and employee practices. In addition, take into account external factors, such as third-party integrations, that could be entry points for attacks.
Evaluate the existing security measures in place
After identifying vulnerabilities, it is time to check the effectiveness of the current security measures and practices that your organization uses. For this, you need to review security policies, incident response plans and employee training. Make sure that these align with the best practices in the industry and comply with the regulatory requirements.
You also need to make sure that employees are consistently following cybersecurity policies and procedures. Determine how your organization enforces the policies and security measures, which could be firewalls, antivirus programs, access control, intrusion detection systems, user training and encryption mechanisms.
This will enable you to identify areas that require improvement or updates. Be sure that you do not skip this step as it serves as a foundation for developing an effective and robust cybersecurity strategy.
Developing a cybersecurity strategy
To improve the digital security of your organization, establish clear objectives and goals. Make sure that these goals are specific, measurable, achievable and relevant. That way, you can focus on addressing the most critical risks within the business. For instance, if your goal is to reduce the amount of successful phishing by a certain percentage, you would need to enhance the data protection measures that your company uses or improve the incident response time.
You cannot develop an effective cybersecurity strategy if you do not involve key stakeholders in your organization. Make sure that they are part of the process when you establish the goals. That way, you can rest assured knowing that the cybersecurity strategy aligns with business objectives. This will, in turn, get support from C-suite and decision makers.
Create a cybersecurity policy and incident response plan
This policy is the basis for establishing a secure environment in your company. It outlines the guidelines, procedures and responsibilities of cybersecurity practices.
The policy should cover data protection, access control, employee responsibilities, incident reporting procedures, and acceptable use of the organization’s technology resources. With more companies adopting working from home, you may also want to create a section in the policy that covers this part.
Ensure that the policy is clear, to the point, and easily accessible to all employees. Review the policy periodically so that you can update it as threats and regulations change.

Besides having a cybersecurity policy, you must also develop an incident response plan. This plan outlines the steps to be taken if a cybersecurity incident, such as a data breach or malware attack, occurs. The plan should include procedures to identify, contain, mitigate and recover from an incident. It should clearly define roles and responsibilities, communication protocols, and coordination with external stakeholders such as law enforcement or cybersecurity experts.
To ensure that your incident response plan is effective, conduct regular testing and simulation exercises. This will also help employees become familiar with their roles and responsibilities when a cybersecurity incident takes place.
Educate employees on the best practices
You can have the best cybersecurity policy and strategy, but it will not be effective if employees are not aware of the common cyber threats. Cybercriminals often exploit human error and a lack of awareness to gain unauthorized access to sensitive data or compromise systems.
When employees become aware of these threats, they transform into the first line of defense to prevent cybercrimes and incidents.
So, take the time to educate employees about phishing attacks, malware, social engineering, ransomware and password attacks. Get into the details so that employees know the techniques that attackers use. These can include deceptive emails, fake websites or suspicious attachments. You can provide real-life examples and case studies to help employees understand the potential consequences of falling victim to these threats.
You can boost employee awareness through regular training sessions and workshops. You can cover different topics related to cybersecurity, such as safe browsing practices, password hygiene, data handling and protection, secure remote working practices, and email security.
Remember, you have to customize the training based on the different roles and responsibilities of employees. For instance, employees in the finance department require additional training on how to identify and prevent fraud. On the other hand, employees in the IT department need technical training on how to secure network configurations and incident response.
When employees become aware and accountable, they prioritize cybersecurity in their daily activities as well as decision-making. Ensure that the employees feel comfortable about reporting security incidents or suspicious activities. They shouldn’t be penalized for reporting.
Implement strong access control measures
Just like your employees, passwords are the first line of defense against unauthorized access to sensitive information and systems. Therefore, make sure that your organization has a policy that enforces strong passwords so that they cannot be exploited by cybercriminals. Furthermore, make sure that employees change their passwords every 90 days. This works to mitigate the risk of compromised passwords.
You also need to take measures to avert unauthorized access to sensitive data and systems. You can do this by implementing multi-factor authentication. This adds another layer of security as users have to provide multiple forms of identification for access. You can use two-factor authentication, biometric authentication or smart cards that generate unique codes for authentication.
It is also advisable to review and update user access privileges. Access should be granted on a need-to-know basis. This ensures that each employee has access to the resources they need to perform their work and carry out their responsibilities. This is the reason why many companies implement role-based access control. If an employee no longer needs access to specific information, it will come out during the review process. At that point, you can remove that employee’s access privileges.
Update and patch software and systems
In a digitally connected world, businesses cannot function without software and digital systems. To ensure that software and systems are secure, it is essential to update them with the latest security patches and updates.
As a cybersecurity specialist, it’s necessary to stay current with industry news and developments. This helps you learn about the latest software vulnerabilities and the patches and updates that vendors release to address them.
To streamline the process of updating and patching software and systems, you can implement automated patch management systems. That way, you do not have to worry as these systems will ensure that any update or security gets deployed across the network without a problem. You can make system administrators responsible for monitoring, scheduling and deploying patches from a central location.
In addition, make sure that you conduct regular vulnerability scans and penetration testing. This enables you to identify possible weaknesses in software and systems. It allows you to identify vulnerabilities that may not have patches available as yet or that could arise due to human error or misconfiguration.
Employ measures to secure the network infrastructure
To secure the network, you need firewalls, intrusion detection systems, and intrusion prevention systems. This helps to monitor and control network traffic, detect and prevent any unauthorized access, and avert potential security breaches.
Another way to secure the network is by encrypting sensitive data and communication. That way, an unauthorized person cannot get access, and the data or communication cannot be intercepted during transmission.
Make sure that data stored on servers and databases are encrypted. You can do this with the help of encryption algorithms. Also, implement secure communication protocols, such as Secure Sockets Layer (SSL), so that they encrypt data that is transmitted over networks.
You can also consider network segmentation to limit access in case of a breach. This involves dividing a network into smaller parts that are isolated. This, in turn, restricts access to other parts of the network. If a breach takes place, network segmentation ensures that the effect is limited.
Disaster recovery plan
Cybercriminals are constantly using new techniques and methods to get access to sensitive data – and, as any cybersecurity specialist will tell you, the security measures that you deploy are not 100% foolproof. So, assuming that a cybercriminal may get access to the data, you need to have measures in place.
The first step is to identify data that your organization needs to keep the business running. This data should be backed up regularly. The backup schedule should be based on the importance of the data and how frequently it changes.
Instead of using the same storage device as the existing data, it is advisable to store the backup data separately. This is where cloud storage solutions and off-site backup help. That way, if theft, fire, flood or a breach occurs and prevents your organization from accessing the primary data, your company can still operate as it will be able to use the backed-up data.
To ensure that your company can operate even after falling victim to a disruptive incident, create a disaster recovery plan. The plan lists step-by-step actions that decision makers and employees need to take if an incident occurs.
It is a good idea to test and update the disaster recovery plan regularly. That way, you can ensure its effectiveness and identify areas for improvement. As your company’s business requirements evolve, you may have to update the plan accordingly.
These are some of the ways that you, as a cybersecurity expert, can help your organization combat cyber threats. Remember that cybersecurity measures are an ongoing process that requires constant monitoring, adaptation and improvement as cybercriminals keep using newer methods.